 Okta SCIM Provisioning
Okta SCIM Provisioning
Available on: Enterprise Edition>= 0.18.0
Sync Users and Groups from Okta to Kestra using SCIM.
Prerequisites
- Okta Account: an account with administrative privileges to configure SCIM provisioning.
- Enable multi-tenancy in Kestra: tenants MUST be enabled in Kestra to support SCIM provisioning. You can enable tenants by setting the
kestra.ee.tenants.enabledconfiguration property totrue:
kestra:
ee:
tenants:
enabled: true
Kestra SCIM Setup: Create a New Provisioning Integration
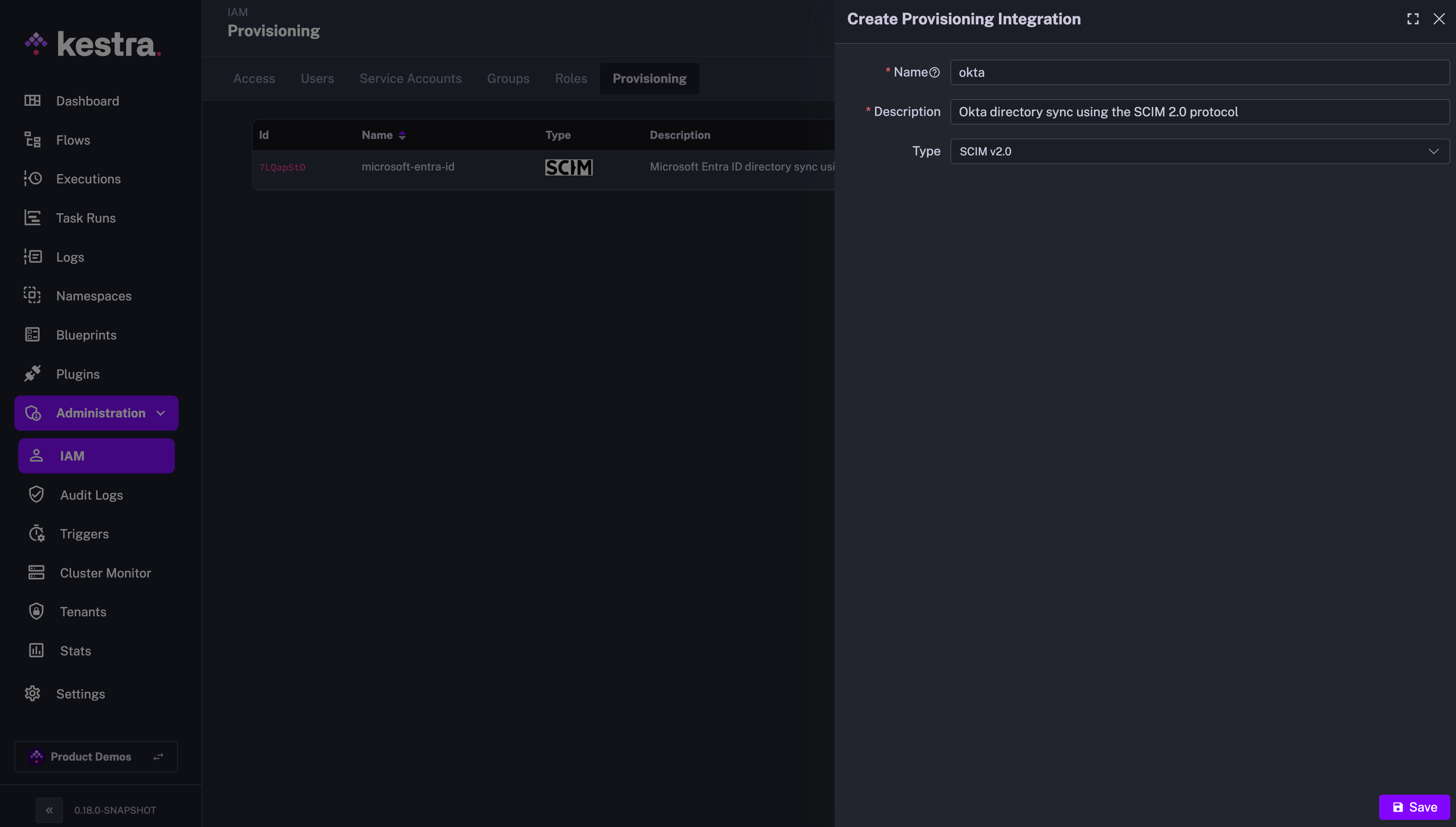
- In the Kestra UI, navigate to the
Administration→IAM→Provisioningpage. - Click on the
Createbutton in the top right corner of the page. - Fill in the following fields:
- Name: Enter a name for the provisioning integration.
- Description: Provide a brief description of the integration.
- Provisioning Type: currently, we only support SCIM 2.0 — leave the default selection and click
Save.
The above steps will generate a SCIM endpoint URL and a Secret Token that you will use to authenticate Okta with the SCIM integration in Kestra. Save those details as we will need them in the next steps.
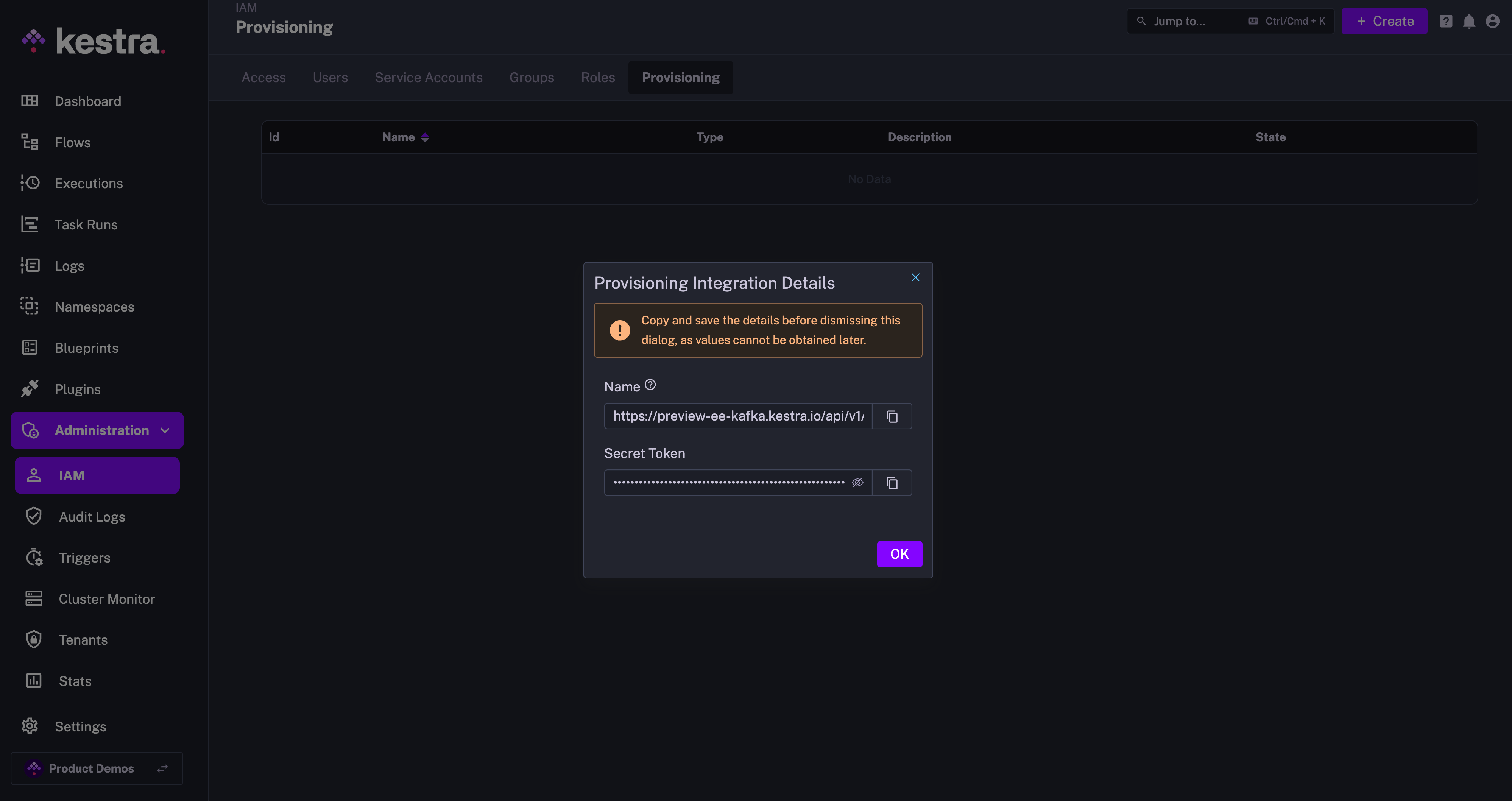
The endpoint should look as follows:
https://your_kestra_host/api/v1/your_tenant/integrations/integration_id/scim/v2
The Secret Token will be a long string (ca. 200 characters) that will authenticate requests from Okta to Kestra.
Enable or Disable SCIM Integration
Note that you can disable or completely remove the SCIM Integration at any time. When an integration is disabled, all incoming requests for that integration endpoint will be rejected.
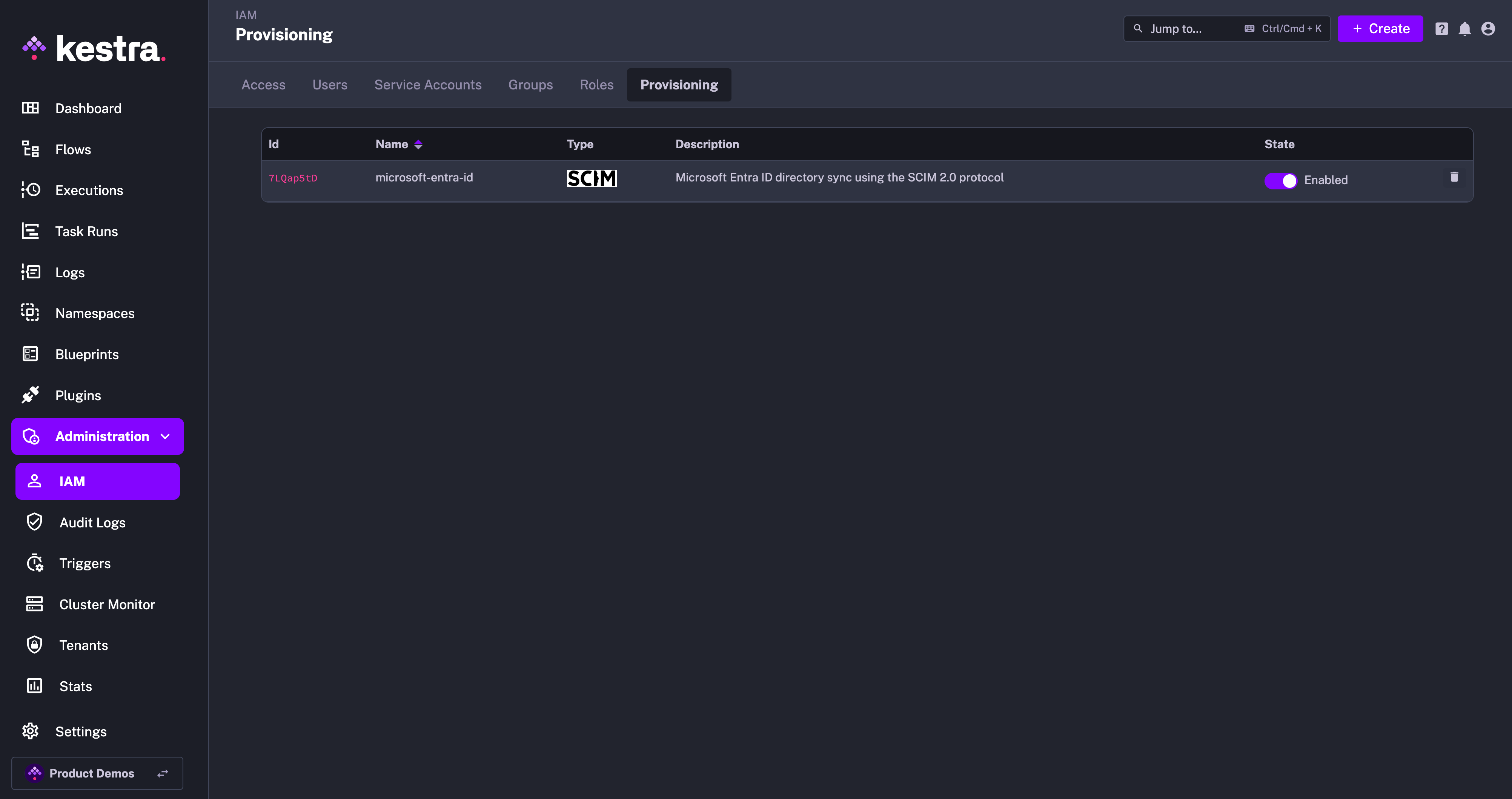
At first, you can disable the integration to configure your Okta SCIM integration, and then enable it once the configuration is complete.
IAM Role and Service Account
When creating a new Provisioning Integration, Kestra will automatically create two additional objects:
- Role
SCIMProvisionerwith the following permissions:GROUPS:CREATE,READUPDATE,DELETEUSERS:CREATE,READ,UPDATEBINDINGS:CREATE,READ,UPDATE,DELETE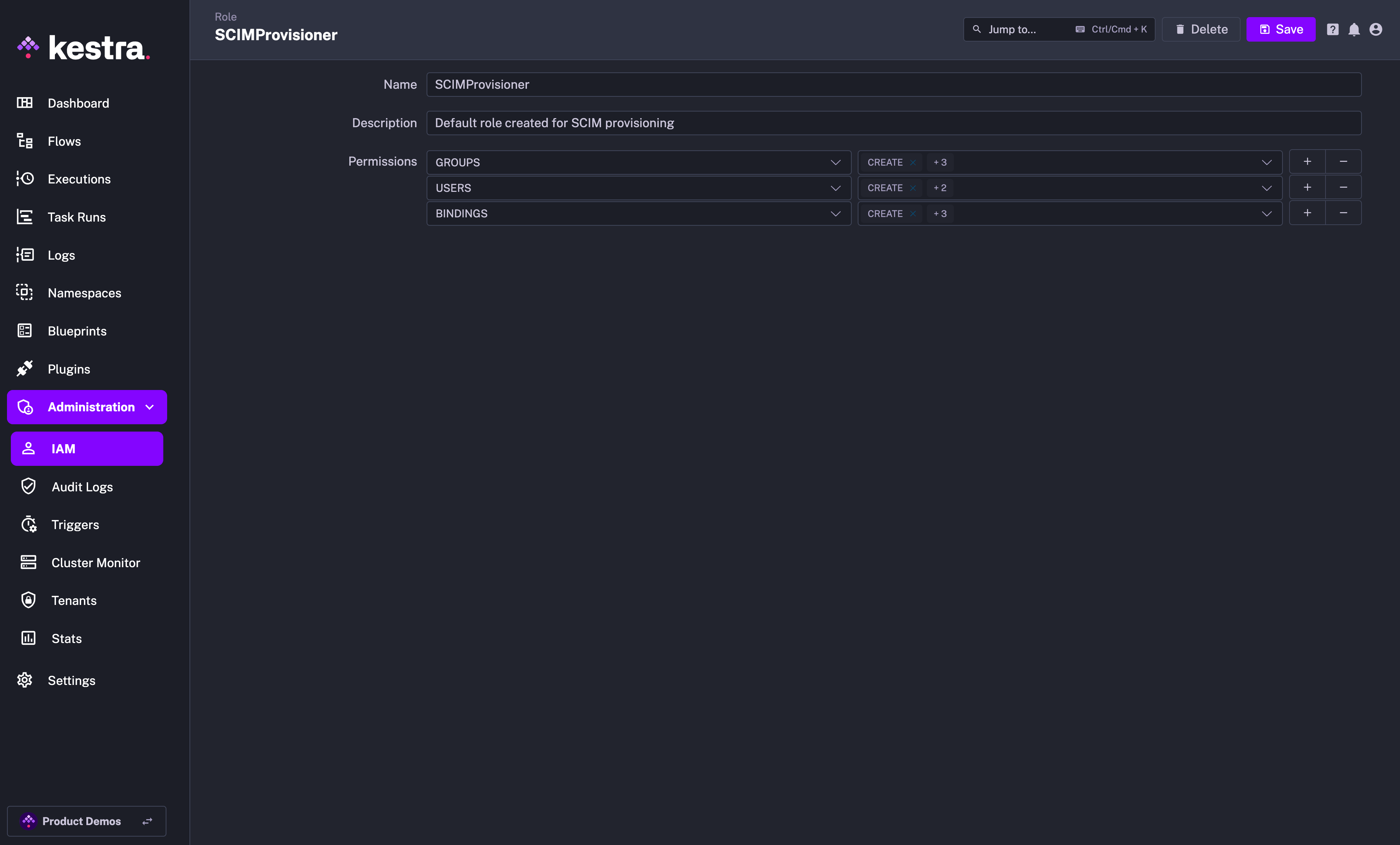
- Service Account with an API Token which was previously displayed as a Secret Token for the integration:
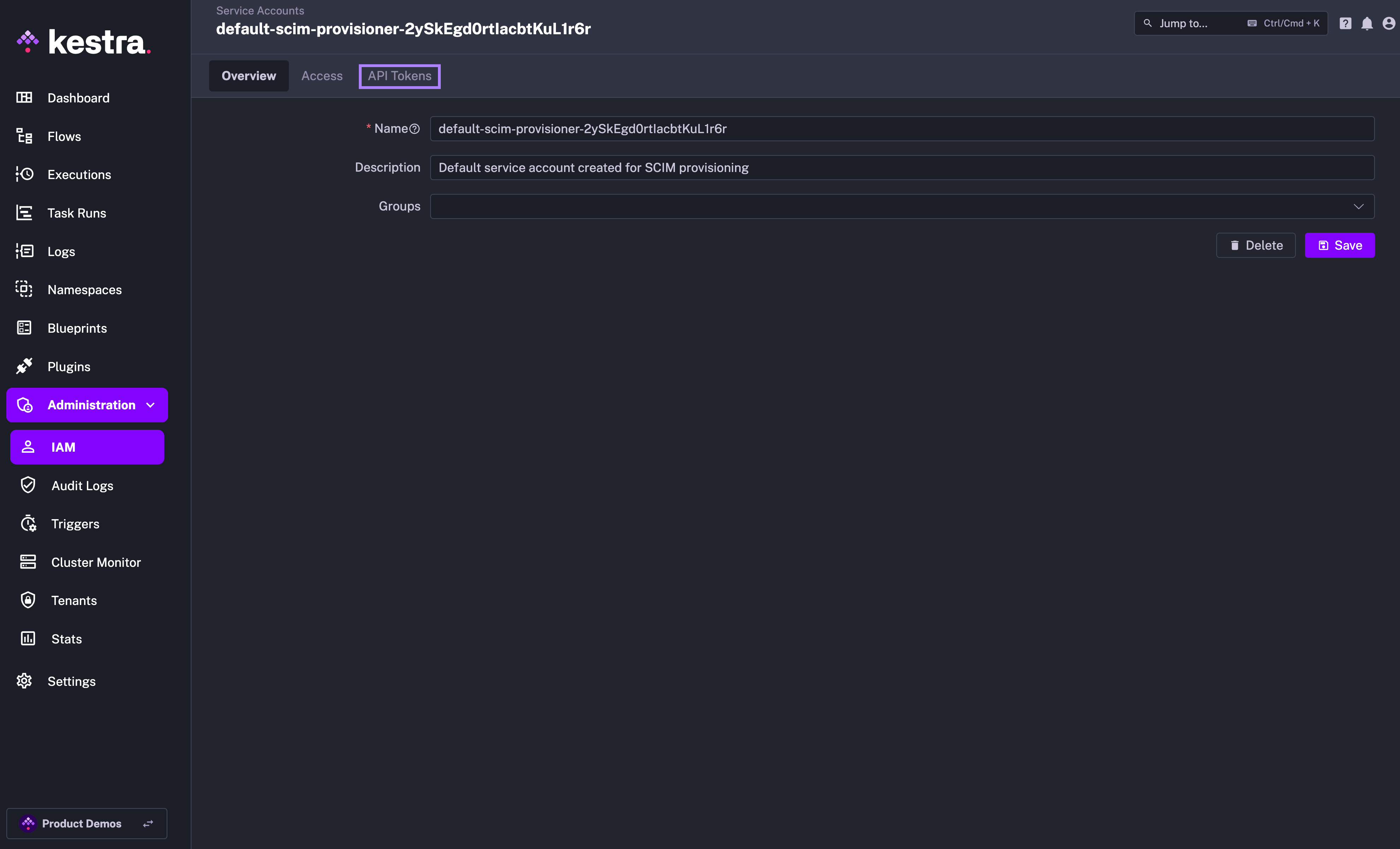
Why the SCIMProvisioner role doesn't have the DELETE permission for USERS? This is because you cannot delete a user through our SCIM implementation. Users are global and SCIM provisioning is per tenant. When we receive a DELETE query for a user, we remove their tenant access but the user itself remains in the system.
Okta SCIM Setup
- Create an App Integration:
- Navigate to Okta Admin Console → Applications → Applications.
- Click on "Create App Integration" and then select:
- Sign-in Method: OIDC - OpenID Connect
- Application Type: Web Application
- Then on the next page:
- Give your application a name, e.g.
Kestra - Grant Type: Client Acting on behalf of itself → Client Credentials → True
- Login
- Sign-in redirect URIs → http://
/oauth/callback/okta - Sign-out redirect URIs → http://
/logout
- Sign-in redirect URIs → http://
- Give your application a name, e.g.
- Once application is created, select it in the Applications view and take note of the client ID and client secret.
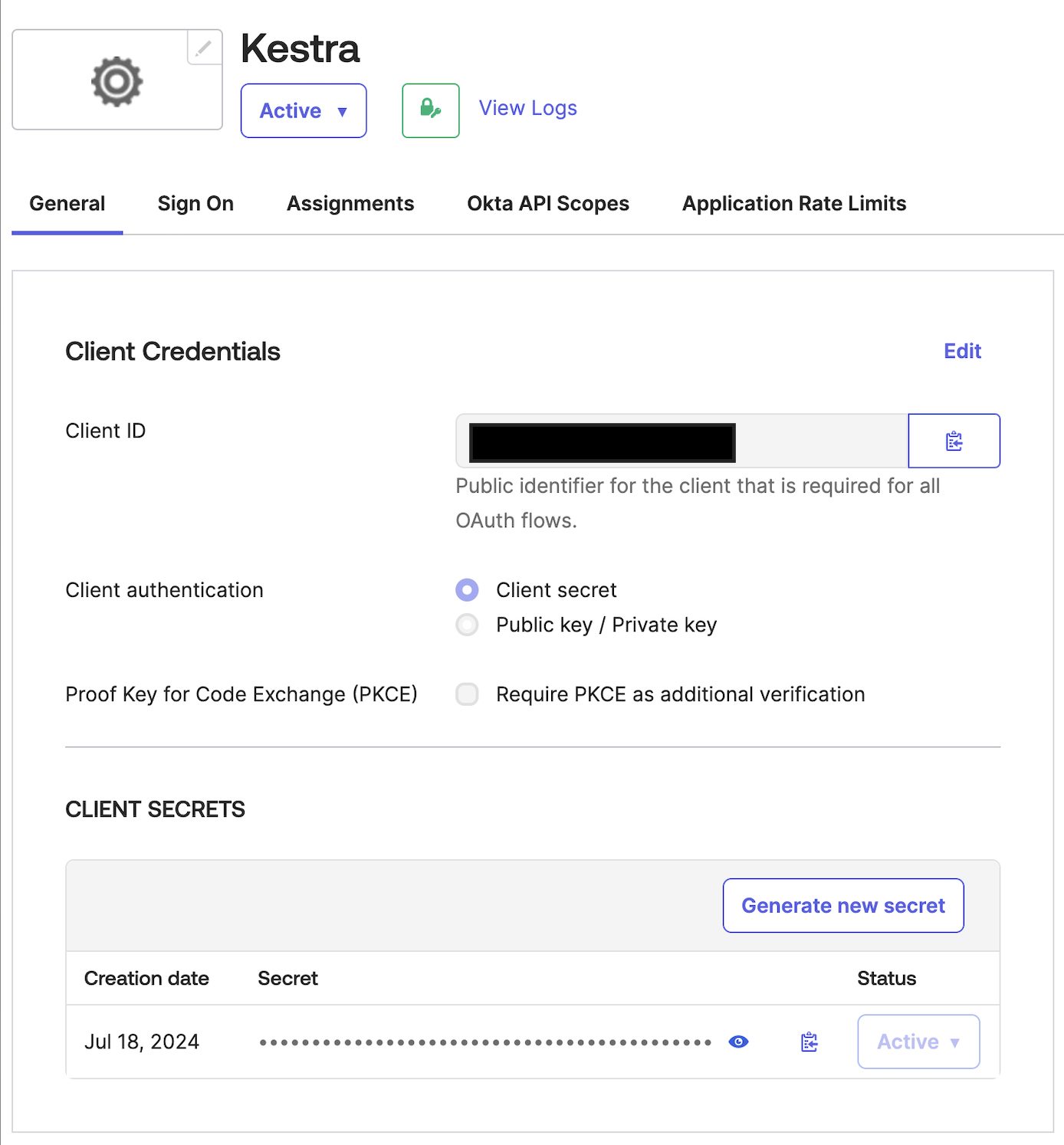
- Configure Okta in Kestra:
- With the above client ID and secret, add the following in your Kestra Micronaut configuration:
yamlmicronaut: security: oauth2: enabled: true clients: okta: client-id: "CLIENT_ID" client-secret: "CLIENT-SECRET" openid: issuer: "https://{okta-account}.okta.com/"- Enter the SCIM endpoint URL and API token provided by Kestra.
- Configure SCIM 2.0 in Okta:
- In Okta, navigate to Applications → Applications → Browse App Catalog
- Search for SCIM 2.0
- Select SCIM 2.0 Test App (OAuth Bearer Token)
- in Sign-in options select Secure Web Authentication → user sets username/password
- Click Done
- Select the integration you have just created, then enter the
Provisioningtab. - Fill in the Endpoint URL you obtained from Kestra into the
SCIM 2.0 Base Urlfield. Enter the Secret Token generated in Kestra into theOAuth Bearer Tokenfield. - Finally, click on the
Test API Credentialsto verify the connection.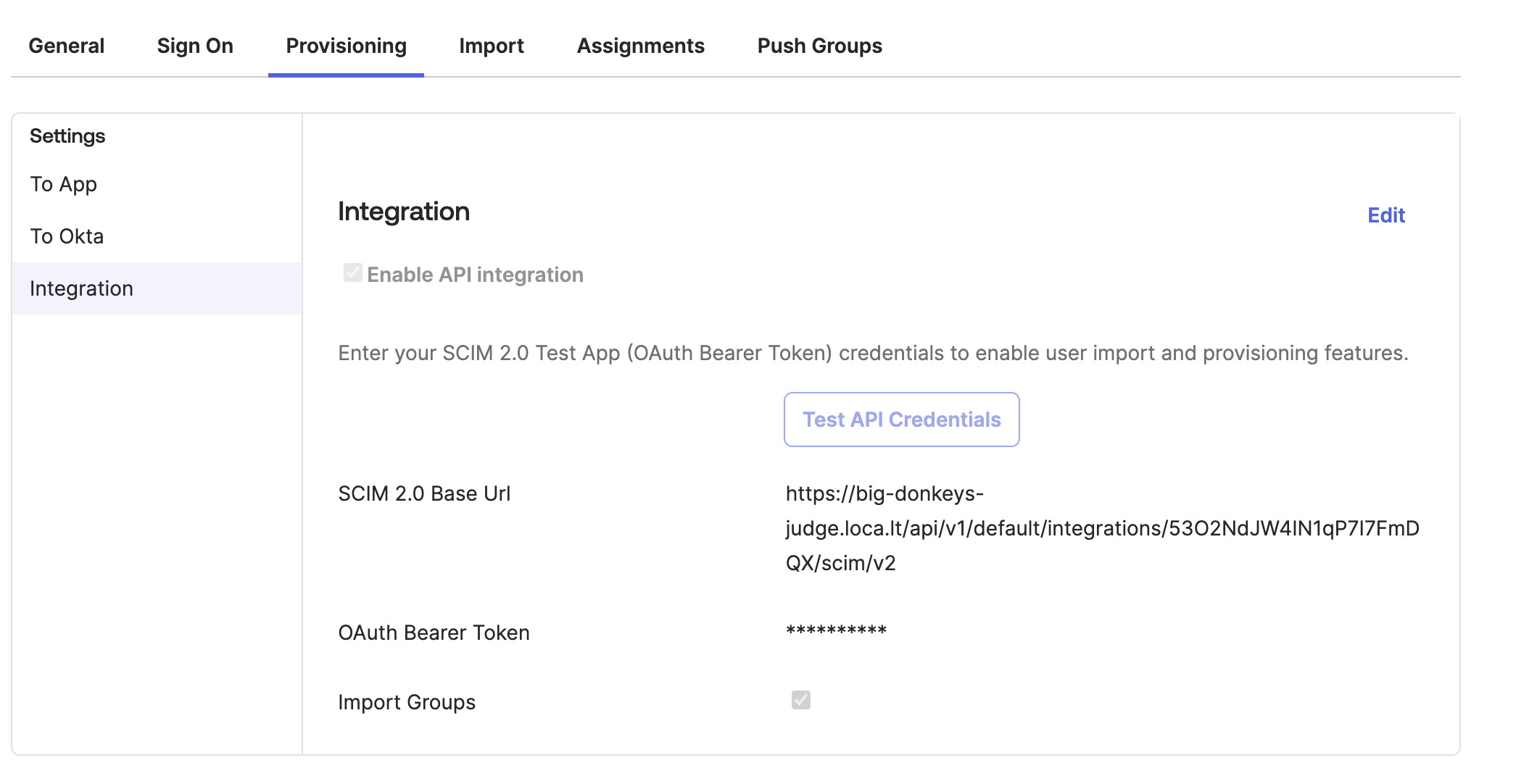
- Map Attributes:
- Select “Push Groups” and choose the Groups you wish to push to Kestra.
- Perform a test to ensure the mappings are correct and data is syncing properly.
- Enable Provisioning:
- Enable the provisioning integration toggle in the Kestra UI to begin automatic synchronization of users and groups from Okta to Kestra.
Additional Resources
Was this page helpful?